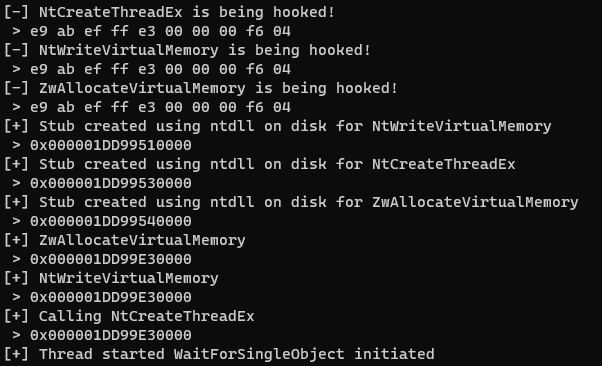
I previously wrote an article on how to potentially detect SysCall hooking from C# so the operator can make an informed decision on whether to migrate processes or whether EDR will have a good chance at detecting their malicious activities. In order to write this post I have read through many great resources by otherContinue reading “Understanding SysCalls Manipulation”
Category Archives: red team
SharpEDRChecker
Problem Statement Endpoint Detection & Response (EDR) Tools are now hiding themselves under different aliases, running at different layers of the system (kernel, user etc.) and on top of that, more and more products with different nuances are hitting the market all the time. But why does this matter? Situational awareness is critical to theContinue reading “SharpEDRChecker”
Worried about EDR hooking catching you out?
This post and subsequent code snippets will help you quickly assess whether EDR is loaded into your process (without a debugger) and performing user-level hooking on important functions that you may wish to use, e.g. process migration using ZwOpenProcess and ZwCreateThreadEx. When red teaming in a new environment we always need to perform situation awareness.Continue reading “Worried about EDR hooking catching you out?”
PoshC2 Shellcode and Binary Patching
TL;DR – This article is a short run through of how PoshC2‘s shellcode is automatically generated on the fly using binary patching without the need for continued re-compilation. We’ll also go over how we use GitLab CI/CD pipelines to generate the payload files and create the artefact files inside the resources folder, specifically shellcode! DevOpsContinue reading “PoshC2 Shellcode and Binary Patching”
To Be A CISO For A Day
A lot of the top-tier companies that I work with have fallen into the same trap of running a compliance driven security function which means policies are created purely to be compliant and not necessarily adopted or fully integrated by the organisation for security purposes. Policies and procedures is a great thing and provide aContinue reading “To Be A CISO For A Day”