I previously wrote an article on how to potentially detect SysCall hooking from C# so the operator can make an informed decision on whether to migrate processes or whether EDR will have a good chance at detecting their malicious activities. In order to write this post I have read through many great resources by otherContinue reading “Understanding SysCalls Manipulation”
Category Archives: blog
SharpEDRChecker
Problem Statement Endpoint Detection & Response (EDR) Tools are now hiding themselves under different aliases, running at different layers of the system (kernel, user etc.) and on top of that, more and more products with different nuances are hitting the market all the time. But why does this matter? Situational awareness is critical to theContinue reading “SharpEDRChecker”
EventLog Searcher
This post and subsequent code snippet will help you quickly find where users have logged on by searching through the system event log for event ID 4624 across multiple hosts in a threaded fashion for both speed and flexibility. User hunting is often the most time consuming part of red teaming and hopefully this willContinue reading “EventLog Searcher”
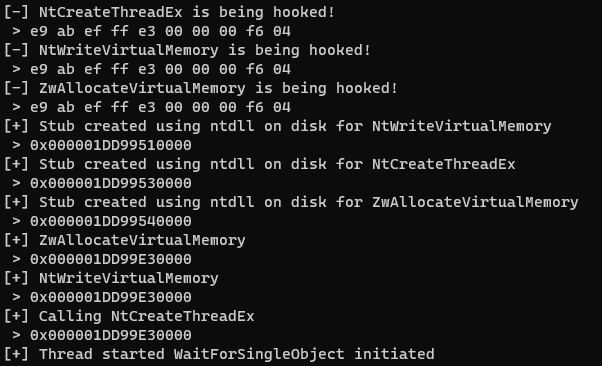
Worried about EDR hooking catching you out?
This post and subsequent code snippets will help you quickly assess whether EDR is loaded into your process (without a debugger) and performing user-level hooking on important functions that you may wish to use, e.g. process migration using ZwOpenProcess and ZwCreateThreadEx. When red teaming in a new environment we always need to perform situation awareness.Continue reading “Worried about EDR hooking catching you out?”
To Click or Not to Click?
When looking at entry points used by APT groups and cyber criminals, a large number of these compromises use phishing as the initial delivery vector. It makes sense, email is now an intrinsic part of how we interact with the world and therefore it is expected that we will regularly see communication from people we know and people we don’t landing in our inbox right on our front door step.